In case the Apple Watch has lost connectivity to the phone it seems to send an advertisement frame, which is erroneously interpreted by your router as iBeacon advertisement.
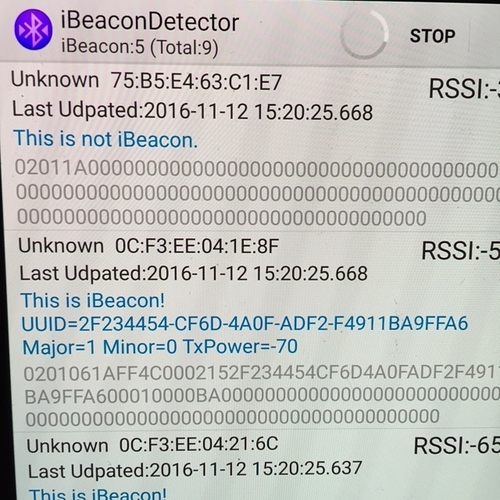
As you can see from the photo attached, the advertisement frame in question is the one sent by the MAC starting with 75:B5. The sniffer app does not identify this as an iBeacon, but your router does. It somehow mixes a couple of things then: It uses the MAC, but the message body of another iBeacon.
So this is the raw_beacons_data element of the Apple Watch transmission, which is erroneously reported as iBeacon (as an RadBeacon). In fact I have 5 other RadBeacons around, one of them has major 4 and minor 0, which is reported herein:
“773BA203025C2F234454CF6D4A0FADF2F4911BA9FFA600040000BAFFB8”
You see that the MAC doesn’t match the photo. This is Apple’s MAC address spoofing: They always use another MAC with every new round for privacy reasons.
But the pattern is repeatable: Whenever I switch BT off on my iPhone, the watch starts to cry for the phone. These packages are then mixed with any other advertisement frame in your reports, so that it appears as an RadBeacon in your reports.
Right now I made another test:
“79DA4359EF942F234454CF6D4A0FADF2F4911BA9FFA600040000BAFFBD”
Regards
Do you set the scan mode to “RAW” mode for the sniffer? It will scan all BLE advertisement data if it’s.
No, the setting is “Full mode” (which might be a superset of Raw-Mode, don’t know), but this is not the point: The problem is, that the “non-iBeacon-advertisement” of my iWatch appears as a RadBeacon. There is something going wrong in the firmware of the router, it seems.
Regards
Do you mean WiFi iBeacon Receiver got some wrong data and upload to remote MQTT broker? Could you please also provide sample wrong datas when your iWatch advertised?
I did already. I my initial post. Please check the screenshot of an Android device, which sees the Apple watch advertisement. This is the first entry. It is full of NULL. Nevertheless in the package my MQTT broker gets from your router the same MAC appears as and RadBeacon:
“773BA203025C2F234454CF6D4A0FADF2F4911BA9FFA600040000BAFFB8”
Note: Apple applies MAC spoofing/obfuscation, so the packet’s MAC is not the same as shown in the screenshot, but you will get the point. Somehow it seems, the empty advertisement is merged with the body of a previous frame, or this happens in the BTLE chip, I don’t know your design.
EDIT: If it is possible to get some debug out of your router via SSH on USB, I will be happy to assist you. Use foreverneilyoung at googlemail.com for instructions.
I’m also confused with package. I will contact you with email directly.